Sophisticated technology for advanced security

BTL integrates strict security modules managing authentication, user permissions, and end-to-end communication encryption.
How efficiently?
- Centrally controlled design and development.
- Secure by design.
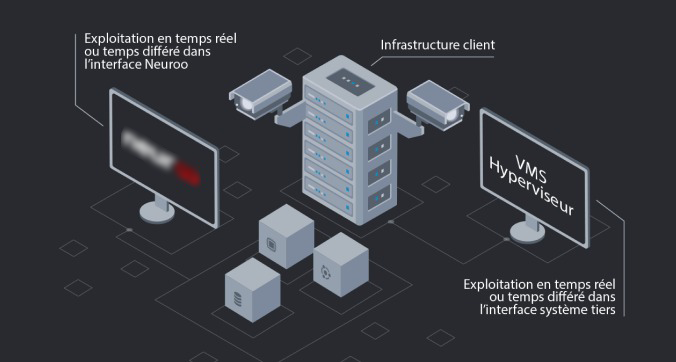
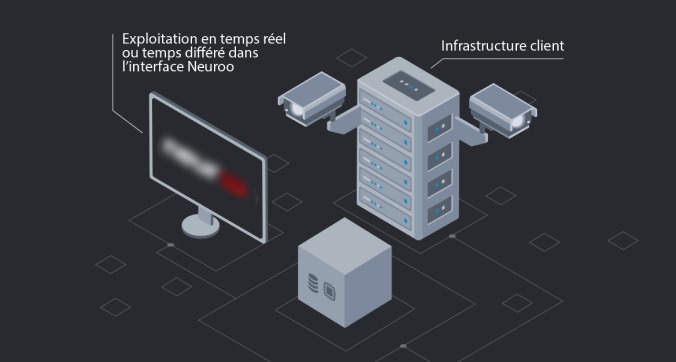
BTL is multi-platform. It integrates perfectly with your virtualized or cloud infrastructure.
With what advantages?
- Flexible deployment based on the existing architecture.
- Interfacing with your existing data capture systems.
- Adapts to any type of existing platform or VMS.
- Integration of standard and proprietary protocols.
BTL natively integrates the components required for application redundancy.
Our application manages automatically load balancing, maintaining all installed modules in an operational state, including real-time analyses.
With what results?
- Scalability of solutions in any type of environment
- High availability:
- Redundancy
- Fault tolerance
- Distributed architecture
- Highly accurate models
BTL solutions are integrated into your architecture without needing a graphics card.
We use thin, virtualizable servers.
You don’t need special hardware. Our solution is 100% compatible with your virtualized environment.